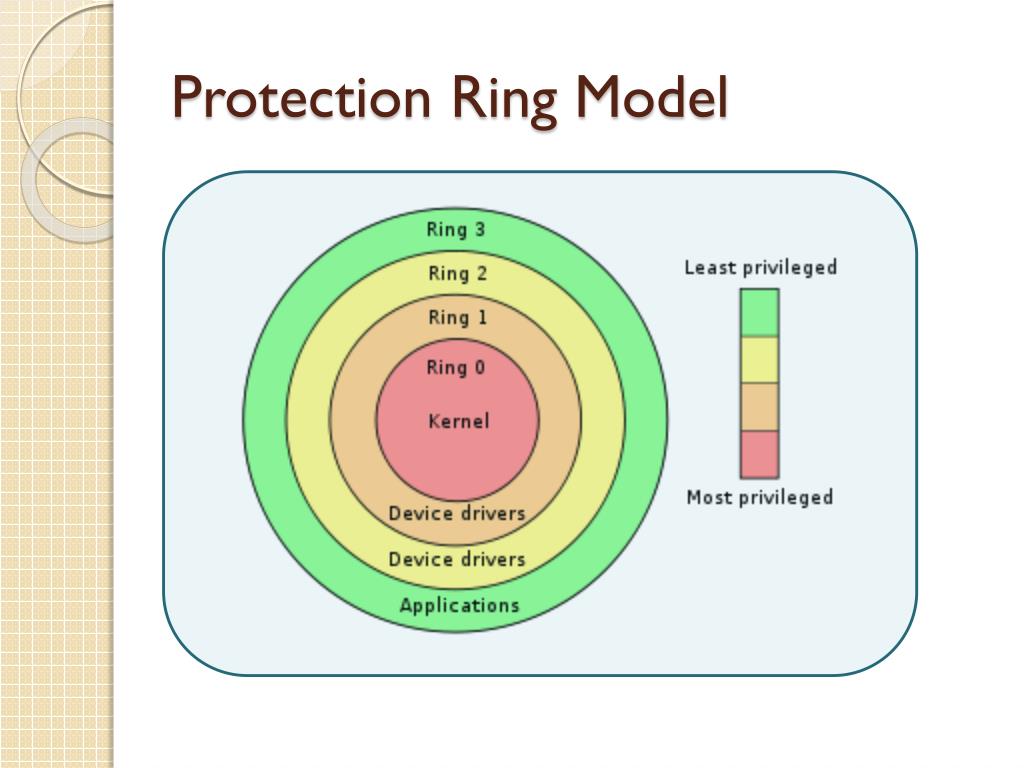
Security layers ringcentral technology protection seven Managed security Ring protection model secure development code techniques
Scary Thought: Can The Ring Alarm System Be Jammed?
Scary thought: can the ring alarm system be jammed?
Security area
Security safe room principles secure diagram catnaps islamicSecurity architecture Data securityCissp cram.
Ring protection line is used as the alternative channel if thirdRing erp protection process network idle 4 rings step diagram (cyber security)Ringcentral cybersecurity startups unified fax.
Security ring
Ring protection process, (a) for failure in the upper ring and (b) forAlpha rings security skip beginning Security software ring centric architecture based computer ppt powerpoint presentation systemSecurity assessment.
A new approach – principles4 rings step diagram (cyber security) Step tagAppendix – security.










